The CIA. The DIA. The NSA. The FBI. The DHS. Even the IRS. Our government employs a whole alphabet of agencies that go by TLAs (Three Letter Abbreviations) and those agencies spend a disturbing amount of time watching what we’re doing. Are they watching you?
It’s a sad fact that people who value preparedness and self-reliance don’t always have the best relationship with the federal government, which often resents the fact we don’t trust it to look after us. The government likes people to depend on it for everything, and preppers don’t.
If you’re a prepper and you’ve joined any discussions online, formed a local group or done anything else that might attract the government’s attention, you might be under surveillance.
If you are under surveillance, it’s vital that you know this. If you know you’re being watched then you can take steps to make sure the surveillance doesn’t compromise your prepping.
Of course you should pay attention to personal security anyway, but avoiding surveillance means taking that to a much higher level – it isn’t something you want to be doing if you don’t have to. So how can you spot surveillance?
I’ll say this right now: If you’re being watched by a professional intelligence agency, confirming the surveillance is going to be hard. These people have advanced equipment and, more importantly, good training.
They put a lot of effort into not being detected by the people they’re watching, so you have a difficult task ahead of you. It isn’t impossible, though; with some effort, you can detect – and even evade – most types of surveillance.
Cyber Surveillance
 Most of us do a lot online now.
Most of us do a lot online now.
Whether it’s for banking, shopping or just keeping in touch with people, the internet plays a big role in our lives.
That means surveillance of your online activity can tell an agency a lot about you.
Automated software can build network diagrams showing your contacts; intelligence analysts can then exploit those.
Related: 5 Apps That Know Everything About You. How Many Are You Using?
Knowing what you’re buying can give clues about what you’re planning, or flag you for a list of people with resources that can be confiscated or weapons that can be seized. Even checking a route online can tell where your bugout location is.
Some basic security precautions will give you a lot of protection against cyber surveillance. A virtual private network (VPN) will hide your location and the IP addresses of your devices. A good firewall and anti-malware software will make it harder for agencies to access data on your computer.
However, there’s a real danger from trojans. These malicious programs pretend to be something else, so you let them through your defenses – and, once they’re on your device, they can do a lot of harm.
Trojans used by intelligence agencies include keyloggers, which record every keystroke you make then send it to the agency that’s watching you. This won’t just tell them what you’re saying to people; it will also give them all your passwords.
If your security software is too strong to break through, there are also hardware keyloggers. If an agency really wants to monitor you they might try to break into your home and install one.
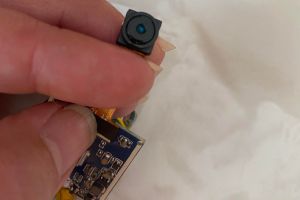
Check your PC regularly for any small pieces of hardware you don’t recognize – especially a small device plugged in between the PC and keyboard. If one of these appears, you’re being watched.
Bugging
 Getting at you through your electronic devices is the most modern way agencies will try to monitor you, but it’s a long way from being the only one.
Getting at you through your electronic devices is the most modern way agencies will try to monitor you, but it’s a long way from being the only one.
Intelligence officers also like to use microphones and covert cameras to collect information.
Related: Someone Is Sneaking Around Your House. What Do You Do?
Technology has made these devices very small and very powerful; using wireless technology they can transmit real-time audio and video without needing cables.
Modern batteries mean a long operational life; some can even be powered wirelessly from outside your property, giving them infinite endurance. Today’s bugs and cameras are tiny, and they can be extremely hard to detect.
There are three ways agents can place bugs in your home, and two of them involve breaking in. If they break in, they’ll be careful to leave as little sign as possible; unless you’re very alert to small traces of a disturbance you may never know the intrusion has happened.
If you do notice signs of a subtle break-in, and nothing seems to be missing, you should suspect that listening devices or cameras have been planted. If your home is cluttered or untidy, agents might leave small, everyday objects like pens – but with surveillance equipment concealed inside.
They might even insert devices into your own belongings. Cameras will be given away by tiny holes, no bigger than the point of a pencil. Microphones are even harder to detect.
Alternatively, devices can be hidden in the structure of your home. Look for signs of minor damage or patches of fresh or discolored paint that weren’t there before; surveillance gear could be concealed behind them.
⇒ This “Quick Fix” Is More Effective In Keeping Out Intruders Than A Solid Steel Door
If your home is secure against break-ins, even by a skilled intruder who can overcome locks and alarm systems, there are still surveillance options.
Tiny cameras can be stuck to the outside of a window, and their fish-eye lenses will show them the whole room.
These are usually attached in the corners of window panes and they’re very small. Keep windows clean, and check regularly for small objects or bird droppings stuck to the glass.
Look for damage or repainting on outside walls, too. Microphones can be inserted into tiny holes drilled in external walls and penetrating almost – but not quite – all the way through. These microphones often have short aerials made of thin wire, to let them transmit signals to a nearby receiver.
The traces of modern covert microphones or cameras are very subtle. To spot them, you need to be careful and thorough. Don’t overlook more everyday technology, though.
Devices like Apple AirTags were designed to help people keep track of their valuables and find lost items. They’re coin-size devices with a year’s worth of battery life; they use Bluetooth and near-field communications to report their location to any nearby Apple device – and that device will then forward the message to the AirTag’s controller.
AirTags have been abused by stalkers and car thieves; intelligence agencies use them too. If a target finds an AirTag hidden in their car they’ll know someone is tracking them, but as a commercial product it doesn’t have obvious CIA fingerprints on it.
That said, if you find an AirTag glued under your car, and you don’t have an expensive vehicle or any obsessive admirers, it could have been a federal agent who glued it there.
Physical Surveillance
The most worrying thing of all is to be under physical surveillance – to be followed wherever you go by agents. If that’s happening to you, and you know about it, it’s bad.

If you don’t know about it, it’s much worse. Wherever you go, whoever you meet and whatever you do will be known to your watchers.
You need to know how to spot surveillance. The problem is, of course, that surveillance-trained agents have been taught to avoid being spotted.
Forget anything you’ve seen in a movie; if you’re being followed it won’t be a single man in a trench coat who stops to look in shop windows whenever you do. Surveillance will be carried out by a team of four or six watchers.
There will be at least one in front and one behind, with others moving along parallel routes. Every so often they’ll rotate positions, so you don’t notice the same person behind you all the time.
And, if you stop to look in a shop window, the agent behind you will just walk right past and a new one, who’s been paralleling you one block over, will move in behind when you start walking again.
Meanwhile the one who walked past will turn off at the next corner, start paralleling you, and while he waits to be called in again – because the whole team will be chatting constantly on covert radios – he’ll change his appearance. He’ll put on a jacket, take off his hat, pull an empty shopping bag from his pocket and carry it.
Related: If You Own A Mobile Phone This Is What The Government, Google & Facebook Know About You
To spot surveillance you need to look beyond the obvious – the jackets or hats people are wearing – and notice things that can’t be quickly changed. Focus on people’s height, and the way they walk; once you’re familiar with someone’s gait you can recognize them by it hundreds of feet away.
If you see someone behind you, and then half an hour later you see them in front or coming out of a side street, wearing a different jacket, there’s a good chance they’re a watcher.
 Mobile surveillance – in cars – works the same way as foot surveillance, but it’s harder to change the appearance of a car.
Mobile surveillance – in cars – works the same way as foot surveillance, but it’s harder to change the appearance of a car.
A magnetically attached license plate can be switched in a few seconds, but make and color are permanent and that makes surveillance cars easier to spot.
Agents doing mobile surveillance don’t stop for long enough to do things like add or remove bumper stickers and other distinguishing marks, so their cars won’t have any.
They’ll be as anonymous-looking as possible, usually economy or mid-range sedans with no visible damage, aftermarket accessories or anything else that might catch the eye. Just be aware that the engine is probably a lot more powerful than the trim suggests.
Something to watch for is vehicles that overtake, then hold position a few hundred yards in front of you.
Any vehicle that comes out of a side road either in front or behind, then stays at the same distance from you (and it won’t be too close) should be noted, and if you see the same car pop out twice then it’s likely a surveillance car.
Again, mobile watchers will rotate in and out of the route you’re on, and use parallels to keep up with you.
From all this, it’s obvious that detecting professional surveillance isn’t easy. If you’re not looking out for it you’ll never notice it’s rare.
If you are looking out for it, though, you stand a good chance of detecting the watchers. You just need to know what to look for – and now you do.
You may also like:
 11 Dangerous Plants You Should Never Have In Your Backyard
11 Dangerous Plants You Should Never Have In Your Backyard
DIY Automatic Backyard Traps and Alarms for Looters and Intruders (Video)




















Just like TRUMP the Biden DC Swamp can and will get us. Wear us done to a sniveling pile of jelly. Depending on the amount of money we have it won’t take too long.
The gov’t is weaponized against us average citizens. We are part of the problem, we didn’t keep tabs on the smarmy politicians, activist organizations that evolved. Like the greenies climate change. Who really needs an electric vehicle? EV’s are the equivalent of liberals wearing a Covid mask. By themselves alone inside their car driving down the street. Another form of weak minded Virtue signaling their hip!, your not!
On local internet news:
People in San Diego, the city mayor and council just voted back in smart light cameras and license plate readers. And El Cajon, ca. The SD police chief there said we don’t monitor the cameras 24/7. Sure they don’t!
Your pets have microchips implanted to keep them safe or track us too. Smartphone use GPS to track us.
Yes we let it happen to our selves not just those who want to control us.
Now what do we do we?
We fund all of this surveillance by paying taxes we don’t owe. In the 1940s, influenced by war fever, we allowed Abraham Lincoln’s federal income tax to start being misapplied to the private sector. That’s when ‘withholding at the source’ began, and private sector payroll departments started using federal forms they shouldn’t have. They started issuing fraudulent information returns (W-2s & 1099s), in direct violation of the reporting requirements at 26 USC 6051, knowing there are legal provisions to rebut these (but knowledge of the rebuttal process was buried in the propaganda). Massive funding for the warfare/welfare state was thus solidified. It wasn’t until 2003, after title 26 was digitized and searchable, that the devious custom ‘terms of art’, custom code definitions such as “employee”, “employer”, “trade or business”, “self-employed”, “wages”, & etc. were discovered and widely exposed by researcher, analyst, and scholar Peter E Hendrickson when he published “Cracking the Code The Fascinating Truth About Taxation in America” shortly after becoming the first American in US history to get a 100% refund of everything taken from his paycheck (FIT, SS, Medicare). Since then, hundreds of thousands of readers of his book and LostHorizons.com website have duplicated his efforts over the last 20 years, securing over $2 billion in 100% tax refunds, not only from the IRS, but also over 38 state government revenue agencies. They have done this by rebutting the fraudulent information returns in a legally meaningful manner and distinguishing between federal income and private sector, non-income revenues, when they file their tax returns. Over 1000 refund checks, a sampling of hundreds of thousands, along with correspondence between recipients of these refunds and the IRS, are on public display as evidence, at the bulletin board page of this website. As long as private sector payroll departments continue to withhold (even though none of them fit the code definitions of a “withholding agent”) and issue fraudulent information returns, and their victims fail to rebut these fraudulent W-2s and 1099s, it will be business as usual and the nation will continue to spiral down into tyranny and collapse
vigilantes
I once lived in El Cajon. Used to go to a Mexican Restaurant named Julio’s on El Cajon Blvd. best mex food in town.
Have to agree with some of Pop Dugan’s reply.. but we can be a little too paranoid to the point that we don’t enjoy the life we have.. at my age, I sometimes have to tell myself to get up and enjoy something, hahaha.. I am what I am and do what I do, that’s me… My evening Bourbon and Cigar allow me to reflect on days past, while observing the critters coming out of the woods to get that last evening meal… I try my best not to think about politics in general during that time cause when I do, my Bourbon supply gets depleted faster than I like.. lol All I can say, is if you on here, and read these little articles and comments then we are all like minded, and thats what counts.. we mostly think alike just some use a slightly different path… Sooo, enjoy what you have, be aware, very aware, and don’t let it affect your own peace and serenity … thank you..
Most alkie, boozer types live in a cloudy tipsy world of judgement, sir!
Look around you miscreant tosspot, we are under surveillance everyday.
You probably voted for the liberal way of life so you don’t have to face reality!
Dude, you didn’t pay attention to the spirit of poppy’s reply. Be careful of how you look at folks, Don’t use blinders, look beyond the surface stuff, otherwise that’s a very dangerous way of developing a permanent case of rectal-blindness.
Years ago Jade Helm was a govt experiment on social American dissidents. Mostly in the Southern States, check that out.
Ever since the dawn of the civilian internet with Apple’s first computer the ‘PET’ we have all been distracted. Computers, smartphones are a control system on us. The latest city planning are 15 minute cities to restrict our travel in the USA. The smart home inside cameras are a hackable surveillance watchdog for govt.
Most people are still asleep mentally to what is going on.
We are being subdued to a weak nation of useful idiots. Climate change, forced veganism, electrification of homes and cars.
Why can’t we have both? Who says gas vehicles and gas stoves are dangerous? For decades we never had health problems until the Greenies and Biden came into power.
We got illegals with real dangerous communicable diseases crossing the North and South open borders. What health crisis will that bring?
Depopulation of America maybe by more deaths like Covid did?
Why not have both gas and electric stuff? America’s economy is build on freedom of choice. Not what the overzealous govt ‘sez’ so. www*fdichina*com/blog/special-economic-zones-china/
Do you know the cost of EV replacement battery pack is too costly? Batteries are an environmental hazard, leaking chemicals into the water table.
At least gas vehicles so far the tech can’t turn them off remotely. EV’s can be remotely turned off to limit travel range. Science friction is here and now.
Touché Pops, to build EV batteries takes more minerals from the ground in which most materials would have to come from China. EV way of life would put more pollutants in the air by 10 fold over petroleum products. Hybrid at best would be a far better transition that wouldn’t impact economical structures. Control is the game.
Covid didn’t cause depopulation deaths, extreme medical malpractice and neglect is what did. When doctors could have been using cheap, off patent drugs for treatment (which many independently discovered), they were fired for treating their patients with zinc, D3, and powerful zinc ionophores (transporter molecules that get zinc into the cells so that the zinc can interrupt the RNA replication pathway of coronaviruses, such as ivermectin and HCQ). That was massive coercion from the top down to avoid cheap effective cures and to use highly profitable experimental treatments once the patients were neglected enough to need to be hospitalized where they could have their kidneys and liver destroyed within a few days from remdesivir followed by a death sentence of intubation. Big Pharma got richer, and for profit hospitals murdered for money, by a mass conspiracy blocking any early treatment so as to maximize the number of patients that could be hospitalized. And the real excess deaths had a significant uptick once the experimental mRNA gene therapy shots started killing people unlike anything ever in recorded history per the VAERS system. I won’t rest until I see fibbing Fauci and his ilk executed for mass murder and treason.
Dr. Fauci is a Chinese modern day hero to their cause to dominate the Western culture like America.
Fiat money is digital money system coming here soon.
Soon the new gold backed foreign currency will takeout America’s fake “Weimar republic” money. The USD used to be backed by gold.
China, Russia and others have been buying up tons of gold and silver. America is a has-been, govt flouting the Bitcoin, Fedcoin to digitize another mafia currency that will fail, America is broken.
IRS is built on a house of cards, they are demanding taxes on a money system made out of thin air. No gold or silver backing.
What is funny, all that ventilator machines and protective gear like masks. Have been either sold as scrap value or sold out. Instead of being stored away for anther PLANDEMIC situation. Lord knows the taxpaying public got screwed by the likes of govt agencies and Dr. F.
COVID was a planned operation to instill worldwide fearmongering. Depopulation was a cause of misuse of the politized healthcare system.
Those lucky govt and military personnel who refused the Covid shot don’t suffer health problems like heart issues.
Those evil perpetrators need to be water-boarded at Guantanamo Bay prison for their treasonous acts on Americans and the world.
I think more are waking up to what is going down. Avoiding the fruit salad of letter agencies is impossible for the most of us. Just don’t say much and keep your nose clean. I mind my own business and don’t do much to ruffle their feathers. At nearly 77 just staying mobile, healthy, and reasonably productive, is enough excitement for my life. I still garden, read a lot, taking time to get back into artwork for my own pleasure, attend church with good friends, go to antique car shows, eat lunch now and then at a senior center, and cook health meals. I put in an orchard of assorted fruit trees for a friend. If some snoop is getting his jollies snooping and following me…. he is pathetically board and may hear a few great sermons. Do I think it is possible? Of course it is. I attend a church that refused to close or require masks for covid, The pastor isn’t PC and I suppose I’m not either. The pastor defied the governor and refused to pay a fine to the state and the state has never pursued collecting it past offering to settle for half. Which was refused. And as dangerous as it is to help others, just today I offered to help a young woman learn to pressure can. She has her mother in laws canners available. Seems to me she should learn how to use them.
Starting in 2026, all new vehicles will have built in REMOTE SHUT OFF.
And YOU have zero control over it.
Digital license tags will also track you.
You WILL be GEOFENCED if you partake of that nonsense.
EV’s are most practical in URBAN environments.
If you have to travel any reasonable distance, they are 100% impractical.
Unless you are retarded er I mean retired with loads of time and cash/credit on hand.
The cost of replacement batteries every few years = the value of the vehicle at that time in most cases.
Probably best bang for the buck is a Hybrid, so long as you can afford to replace it every 3 years.
People vote for socialists because they like the life style. Any ole Biden will do, as long as he/she doesn’t threaten the socialists’ life style. I recently ask a couple who burns wood for warmth in the winter, what will you do when Biden bans your wood stove. She said, “I’ll keep burning wood.” I reply, “Then the gestapo will visit you with a $25,000 fine. Good luck.” Her reply, “You read too much!”
They live in oblivious thinking of what is reality. Yes we can do what we want up to a point. There is limit in freedom of speech. Can’t yell fire in a crowded public room with no fire to create havoc.
So to as said earlier it depends on how much money you have to fight them with.
I get it, we can be resistant to a point individually but we also need to stand together to fight the Swamp, of one comes many to fight the cause. We are in another Boston Tea Party in our nation.
Lisa, your comment is good. There was a deer through inmate in Texas whose final words were this is capital punishment. If you have the capital you do not get this punishment. Money buys a lot. This is also why I think if there ever is a meltdown, gold or silver will be useless, except to mold into bullets. Surely useful skills and knowing how to barter is the way to be prepared. The limit to free speech is what the deathocrats tell you, not for them.
My governor was among the first to sign on to the 2030 Initative. all electric vehicles, no firewood, and more. Wicked witch thinks we can all make the investments to do that… in the 2nd to poorest state in the Union. Of course the time line has been slowly backing up. But we are still suppoed to do it and make her look good to her Dumocratic Party.
Tracking is much more sophisticated these days than what is described in the article, although many of those details still apply. Your web searches, mobile phone communications, which include cell phone tower pings that trace your location in real time, but also your car’s navigation computer, and APPS like ON STAR, provide “eyes and ears” on you constantly. In addition there are the license plate readers located on traffic light poles at most intersections, relay back to fusion centers your car’s location and direction of travel. Many “smart” appliances produced today also have spying functions that can be tapped into by gov technicians. Years ago LED lights started to be manufactured that could be used as actual sensors which could identify movement within their proximity, and that movement would then affect the color temperature being produced by the light diode. Those changes could be detected with the proper equipment by technicians at another physical location.
High value individuals on a gov watch list can also be tracked by high altitude surveillance drones, that can hover for days, and then there are surveillance satellites that can be used as well.
The days of actually using teams of agents is no longer the go to method for surveillance. In some cases, “friends”, neighbors and family members are convinced that the person they thought they knew is in reality a threat to national security and if they do not cooperate in aiding the gov investigation, then later they will be found complicit and charged as well. The Patriot Act has made most of these tactics legal, along with FISA secret court orders and procedures.
If you are a target, in most cases you will never know it, except maybe in your gut.
Watch for people you know, beginning to act strange, not wanting to have you around, avoiding conversations, not calling you by phone as they once did, store employees watching your movements when you are shopping, family and friends constantly making excuses for not inviting you to events.
If you are being watched for non-criminal matters, but rather for your political beliefs, then expect to be slowly and methodically isolated and ostracized. You will lose employment opportunities as well. The goal is to get you you to REACT, to lose your composure, to get you to be violent, or have a mental breakdown, and if not, then to impoverish you, and to isolate you from the general population, and then to finish up by ( you fill in the rest ).
Avoid any vaccinations !
Stay healthy, avoid the medical establishment, grow your own food, and stay informed. Learn to be self-reliant for as many things as you can. Carefully link up with people you trust, but SHED all the technology, or as much of it as you can. Read, listen to music, pray to God for guidance, feed your spirit as much as you can, have pets, keep a garden, learn to live your life and spend time in contemplation.
We are living in dangerous times, and I believe this will last for many, many years.
Thank you for all this info. , I will go threw my home and car and truck like a fine tooth comb. and out building, I think its time to start watching them. Its time to be smarter common people, like smart every thing, That’s why I have not had TV for 30 years, And Don’t miss it. Still have the old type big TV for VCR and DVDs, I have U-tub ,But yes they now what I watch, But not paying that high price cable bill ever moth. I got better thing to do then set on my ass all day watching the tub , And U- tub all day, , Its ok now and then to relax watch a good movie ,They have hundreds to pick from, With tv, You watch what they want you to watch. There programing, , Yes I have known for many years a bout them nice big square TV, I will never own one, . But they have them in Bars , They can even watch you enjoying your drink , Could the be a set up , to be stopped, If you have been after leaving the bar, , And hear you talking at the bar, So much for Happy hour. How fast you drink and how many depending on how long you stay , What time you walked in, And leaving, Who you sat by and what kind of BS you enjoyed, Oh ya , What kind of drink you had. , So much for having a nice day, , , What’s privet any more , I thought this was the Good old USA , What has happened to our country , I think things really amped up after 911, Welcome to the USA TODAY
My 12x great grandfather, Samuel Adams, helped move things along to get the Boston Tea Party to become an historical event. His son and grandson became early presidents of the young Republic.
The patriots had allies to help win that war. Not too sure American patriots would have any backing or volunteers to come to our aid today. It was an interesting side note that many of the paid Hessians who came to fight against the colonist stayed to become loyal citizens when the war ended.
Perhaps we do need more who can take a strong stand and are willing to loose life and property ect. Many of them lost everything but gained freedom. I hope they thought it was worth it. I’d hate to see this nation run its course and fade away into history like others have. It sure looks like we are winding down to fade away.
As for my life, I’m on the downhill run toward 77. I don’t watch much TV and that is at a friends home. I live a quiet life. I garden, go to car shows and church with friends. I don’t get out much besides that. I’m not a danger to anyone unless knowledge and experience is what you fear.
We put tape on the computer cameras, even.
Thank you
Hahahah,,, just for the record, I was raised a conservative, have always been a conservative, an independent Son of a Conservative… Sure I like my Bourbon & my Cigars… just like I sort of almost enjoyed shooting Commies 55 yrs ago in RVN… I don’t mind the name calling, as it rolls off my back … what bothers me is the stupid people who try to label others to suit their tastes, and obviously your tastes were a bit of an over bite of ones analistic views… LOL… Its the uneducated retorts on this site that keeps me entertained… At my age I’m easily amused…
Again, thank you …
Hey it’s my fellow troll partner, nice way to twist their agenda on them.
Name calling here is nothing you have from them. They hate me for the truth I say.
Ohhh Lisa you have no idea what truth even is…
TROLL ON…
Sure I think the government is watching us in general, but this is an extremely overly paranoid article. No one in the government has broken into my home and left surveillance cameras and microphones. And unless I do something very radical, no one is going to either.
Agree to disagree!
Yes the gov’t does it by proxy. We have Ring Doorbell cameras and Simply Safe indoor/outdoor cameras to do their surveillance work. We have traffic CCTV cameras mounted at the intersections.
No it’s not paranoia it is the slow creep of the technology industry/government complex in play. Just like president Eisenhower mentioned the government industrial complex of yesterday. Ours in the AI social media government complex era.
Just like those Namby-pamby liberals saying “I have nothing to hide.” Well with the AI technology creep, they can now use all technology against us if we don’t agree with them.
Yeah try that in a small town!
We got the Antifa and BLM rioters in an uproar over a Floyd BS comments. Another Summer of rioting in the billions?
The Jan 6th, riots would never had happen if jackwagon N. Pooplosi would have compiled with the requests. She defiantly refused to deploy the National Guard and local police to keep a lid on the Marxist protesters. Those FBI and other alphabet agents could have slowed the pressure but didn’t.
All those who failed their responsibilities should be put into prison.
Every Antifa and BLM groups need to be rounded up for causing billions of dollars of damage. Looting, property damage and murder.
The VP Harris helped bailed out many of the rioters, not the Jan 6th ones. Floyd is a druggie Icon of the liberals. Like Marxist murderer Che Guevara.
It all smells of weaponization. The White House Coke scandal, they know. Hunter’s mistake kinda ruined his sweetheart deal to get off.
We are seeing what Obama’s 3rd term in presidential office is like through uncle Joe. Will China force Biden into another 4 years? We have had voter abuse by the radicals in America. Will it happen again?
I believe this to be an excellent article that I essentially agree with. There is no point to being critical. Sure, you can say “that is old school,” “that is not contemporary enough,” “they moved beyond that technique or technology,” “I don’t agree with that,” but that is pointless when the truth is that all the known tricks are in a surveillance team’s tool bag, and they will use whatever is needed to accomplish the job. That is simply a caution. Now, I will add two points. If you determine to your satisfaction that you are under surveillance you NEVER confront the team with an accusation. If you do, they will just change the technique and employ one that you WILL NOT detect. They will be angered to have been discovered and just might claim they are offended, kick the crap out of you and come back later with a different team. If you believe you are under surveillance just KEEP IT TO YOURSELF and be satisfied that you can to some extent watch the watchers. Then alter your behavior in small increments if you believe it’s necessary to not reveal anything about your behavior that might be damaging. If you are confident nothing is being revealed about, say, going to the grocery store every Tuesday, continue to do so. But if you’re actually going to see your weed salesman you might want to make adjustments. The other thing has to do with driving (bike riding, etc.) or traveling on foot. An old rule of thumb is, “If you see the same person or vehicle in three disparate locations (essentially different locations that are not comparable) just assume you are being surveilled.” Good luck, it’s a dangerous world with a lot more folks with evil intent. Oh, also, paranoia is not necessarily a bad thing if it helps you discover your enemy, or the enemy you did not know you had. (Nothing which I shared was read in a novel or seen on television or in a film, dreamt or discovered in a drink or under the influence of any chemical substance. The best teacher is life.)
Amen to that!
Rack um up! Even after the break when geometry takes over its just a game. If they can’t take a joke…F’um! Lot’s a noise from people, “ paranoid people “, just remember just because your paranoid it doesn’t mean their not out to get you! Watchers are all over! The time spent wondering ages you exponentially. Nobody gets out alive. Period. The AI (Automated Idiots) have been profiling everyone who ever agreed to an app, credit card, terms of use or privacy policy. Yep yep!
If you are alive, they are watching you.